Dark Web Monitoring vs Dark Web Scan: How to Choose the Right Protection for You
An unfamiliar login attempt or an unexpected password reset can be an early indication that something is not right. Incidents like these often create uncertainty and raise concerns about the safety of your personal data. Over time, this leads to a more important question: whether your information has been exposed in places beyond your visibility and control.
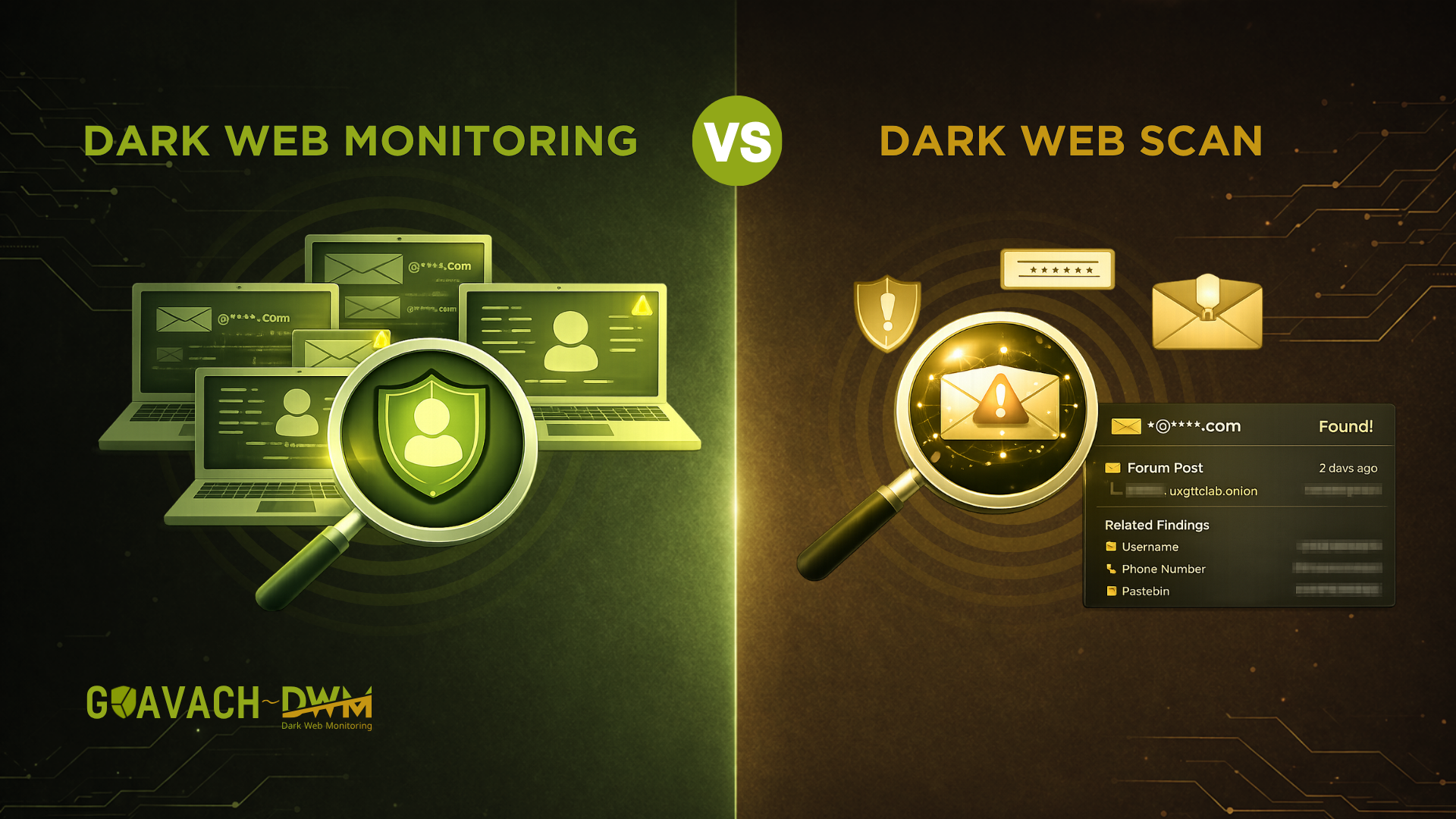
When evaluating potential data exposure, you are likely to encounter terms like dark web scan and dark web monitoring. Although they may appear similar, they operate very differently. Recognizing this difference is important if your goal is to move beyond basic visibility.
What is a Dark Web Scan
A dark web scan is a one-time check that looks for your personal information in known data breach databases. You enter your phone number or email address, and the tool compares it against records that have already been discovered and indexed.
The purpose of a scan is straightforward. It tells you whether your data has already been exposed in past breaches. The results usually include the platforms affected and the type of data involved, such as passwords, usernames, or contact details.
A typical dark web scan helps you:
- Check if your email or phone number appears in the known data breaches
- Identify affected platforms and exposed data types
- Take initial actions like updating passwords
This makes a scan useful as a starting point. However, its usefulness is limited to that moment. It does not track new leaks, and it does not provide continuous monitoring and alerts.
What is Dark Web Monitoring
Dark web monitoring takes a different approach. Instead of checking your emails once, it continuously tracks your data across various sources where leaked information may appear. These sources include forums, underground marketplaces, and leak sites that are not always visible through standard searches.
The key idea behind monitoring is persistence. It runs in the background and keeps scanning over time. If your data appears in a new breach or is discovered in a hidden source, you can get alerts and know about the breach.
Dark web monitoring usually involves:
- Continuous scanning of dark web marketplace and forums
- Detection of newly leaked or recently indexed data
- Instant notifications when your information is detected
This ongoing visibility is what makes monitoring more aligned with how data exposure happens. Breaches are not one-time events, and stolen data often surfaces gradually.
Why Timing Matters More Than Exposure
When it comes to data breaches, timing matters more than most people realize. Many users focus on whether their data is exposed, but the more important question is when they discover it.
Stolen data often does not appear publicly right away. It may be sold privately or shared in smaller groups before reaching known breach databases. By the time a dark web scan detects it, attackers may have already tried to use the information.
This is where the difference between dark web monitoring and a dark web scan becomes important. A scan shows past exposure, but dark web monitoring tracks new threats as they appear. In simple terms, a scan gives awareness, but monitoring enables faster response.
That timing advantage can make the difference between preventing an issue and dealing with its consequences.
When a Dark Web Scan is Useful
A dark web scan is useful as a starting point. If you have never checked your exposure before, it helps you understand whether your data has been part of known breaches and allows you to take basic steps like updating passwords.
It is most useful when you:
- Want a quick snapshot of your exposure
- Have never checked your data before
- Need basic awareness without ongoing tracking
However, its limitation is that results quickly become outdated as new breaches occur, meaning it does not reflect the current risks over time.
When Dark Web Monitoring Becomes More Important
As your online presence increases, your level of exposure also rises. Most people use the same email across multiple platforms, including financial services, social media, and work-related accounts. Each of these connections increases the potential impact of a data leak.
Monitoring becomes more relevant because it provides ongoing awareness instead of a one-time check. This is particularly important for individuals who rely heavily on online services or manage sensitive data.
Dark web monitoring is more suitable if you:
- Use more than one email on a regular basis
- Have financial or work-related data at risk
- Prefer to be notified early instead of discovering issues later
The Real Risk is Delay, Not Just Exposure
When credentials are leaked, attackers often act quickly. They test passwords across different platforms and attempt to gain access before the user becomes aware of the issue.
If you discover the exposure late, you are reacting after potential misuse has already occurred. If you discover it early, you have a chance to secure your accounts and reduce the impact.
This is where monitoring provides a practical advantage. It reduces the gap between exposure and awareness, giving you more control over the situation.
What Makes Monitoring Tools Useful
Different monitoring tools offer different levels of benefit. Their effectiveness relies on how clearly information is shown and how quickly alerts are sent. A useful system should:
- Explain what data was exposed
- Show where the data was found
- Provide context about the risk
- Offer clear next steps
Without this context, alerts can feel vague and difficult to act on.
Solutions like GKavach Dark Web Monitoring address this gap by combining detection with actionable insights. Instead of just notifying you, they help you understand the severity of the exposure and guide you in the next steps. This reduces response time and makes it easier to take immediate action.
Understanding False Positives
It is important to recognize that no monitoring system is perfectly accurate. There may be cases where older breach data is flagged again or where the information is no longer relevant.
In these cases, it is important to assess the alert instead of ignoring it. Reviewing the breach date and checking if the affected credentials are still in use can help determine the risk level.
Why Continuous Monitoring is Becoming the Standard
As data breaches become more frequent and more complex, relying on occasional checks is becoming less effective. The reality is that most users are exposed across multiple platforms, often without realizing it.
Continuous monitoring is increasingly seen as standard practice because it allows users to stay informed and respond quickly before issues escalate.
Conclusion
A dark web scan helps you assess your previous exposure, giving you a baseline and showing if your data has appeared in known breaches.
Dark web monitoring focuses on what happens next. It keeps tracking your data over time and alerts you when new risks appear, giving you the opportunity to respond early.
In an environment where data breaches are frequent and often delayed in becoming public, relying only on a one-time check is not enough. Staying informed over time provides a stronger level of protection.